Blogs
News & Updates
How to Transform User Access Reviews To Meet The Challenges of the Cloud and AI Era
Four transformational approaches to improve the efficacy and efficiency of User Access Reviews - a foundational aspect of Identity and Access Governance Author Ken Foster, VP of IT Governance, Risk and Compliance, FLEETCOR Venkat Raghavan, Founder and CEO, Stack...
Webinar Recap: Shadow Access: Where IAM Meets Cloud Security
Earlier this month, Ken Foster, VP of IT Governance, Risk and Compliance - FLEETCOR and Al Ghous, former CISO Snapdocs, Advisor, and Investor, had an open conversation with our founder Venkat Raghavan about the rampant risks of unauthorized access in cloud...
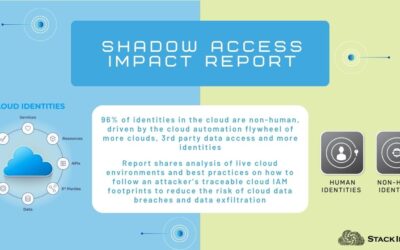
Stack Identity Shadow Access Impact Report: How Identity and Access are Disrupting Cloud Security, Compliance and Governance
Summary: This Stack Identity Shadow Access Report outlines the risks created by thousands of dynamically changing cloud identities and associated access permissions. It provides key statistics and insights on how the security of cloud environments are at risk of the...
Navigating the SOC-2 Process: A Start-Up’s Experience wrt Governance, Administration and Audit
We understand the importance of security and wanted to start with SOC-2 compliance to implement basic security for our environment.
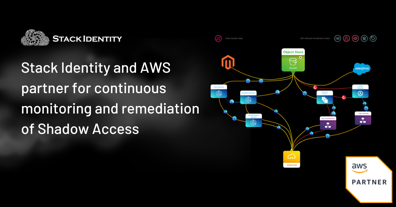
Stack Identity and AWS partner for continuous monitoring and remediation of Shadow Access in public and data cloud environments
Stack Identity has achieved Validated Partner status and passed the AWS Foundational Technical Review for its automated cloud IAM operations platform. The Stack Identity platform detects the dynamically changing yet recurring risk of data exfiltration, and helps...
LastPass Breach Investigation: An Analysis Through the Lens of Cloud IAM Operations
By Venkat Raghavan and Dr.Prakash Shetty This report is an analysis of IAM activities undertaken by the threat actor in the LastPass breach; the source of this analysis is the publicly reported incident timeline from LastPass. Introduction to the Analysis of the...
How PagerDuty and Stack Identity Ensure Timely Notification of Cloud Data Breach Risks
By Stuart Horne Security teams complain that they are overwhelmed with existing cyber security initiatives when it comes to dealing with emerging new attack vectors. Yet one of the newest attack vectors - Shadow Access (resulting from poorly managed IAM operations and...
How To Secure Your Data Supply Chain with an Identity-First Approach
Digital supply chains and data power our digital economy. Conceptually similar to physical supply chains, digital supply chains interconnect various data systems, data providers and data consumers. Many financial services and banking customers need to share sensitive...
Shadow Access in Your Cloud
By Venkat Raghavan, Founder & CEO, Stack Identity Shadow Access is unmonitored, unauthorized, invisible, unsafe and generally over-permissioned access that has grown along with cloud identities, apps and data. Today, identities, human and non-human are...
Guest Post: A Balancing Act – Developer Agility vs Cloud Data Security
By Rupa Parameswaran The cloud software development ecosystem operates in a complex and dynamic environment where identities and access are spread across the different systems and generally operates with overly permissive access with lax identity and access management...